Device Integrity with TROPIC01
Authenticated device, verified firmware and detected tampering.
Device integrity means verifiability of your hardware together with software which it runs. The device boots only authorized firmware and accepts only signed updates. Its cryptographic identity cannot be cloned. Physical or logical tampering gets detected. External systems can verify these properties cryptographically rather than trusting vendor claims.
Software-based integrity mechanisms have fundamental limitations. Attackers can modify firmware before verification code executes. Keys in MCU flash can be extracted with debugging interfaces. Software counters can be reset through voltage manipulation. Hardware roots of trust provide immutable anchors that exist below these attack surfaces.
TROPIC01 makes it extremely hard to boot malicious firmware and provides cryptographic proof of a device's state. If the firmware has security holes, the device remains vulnerable. Integrity is the essential foundation. Without it, any security guarantees built higher in the stack become unreliable.
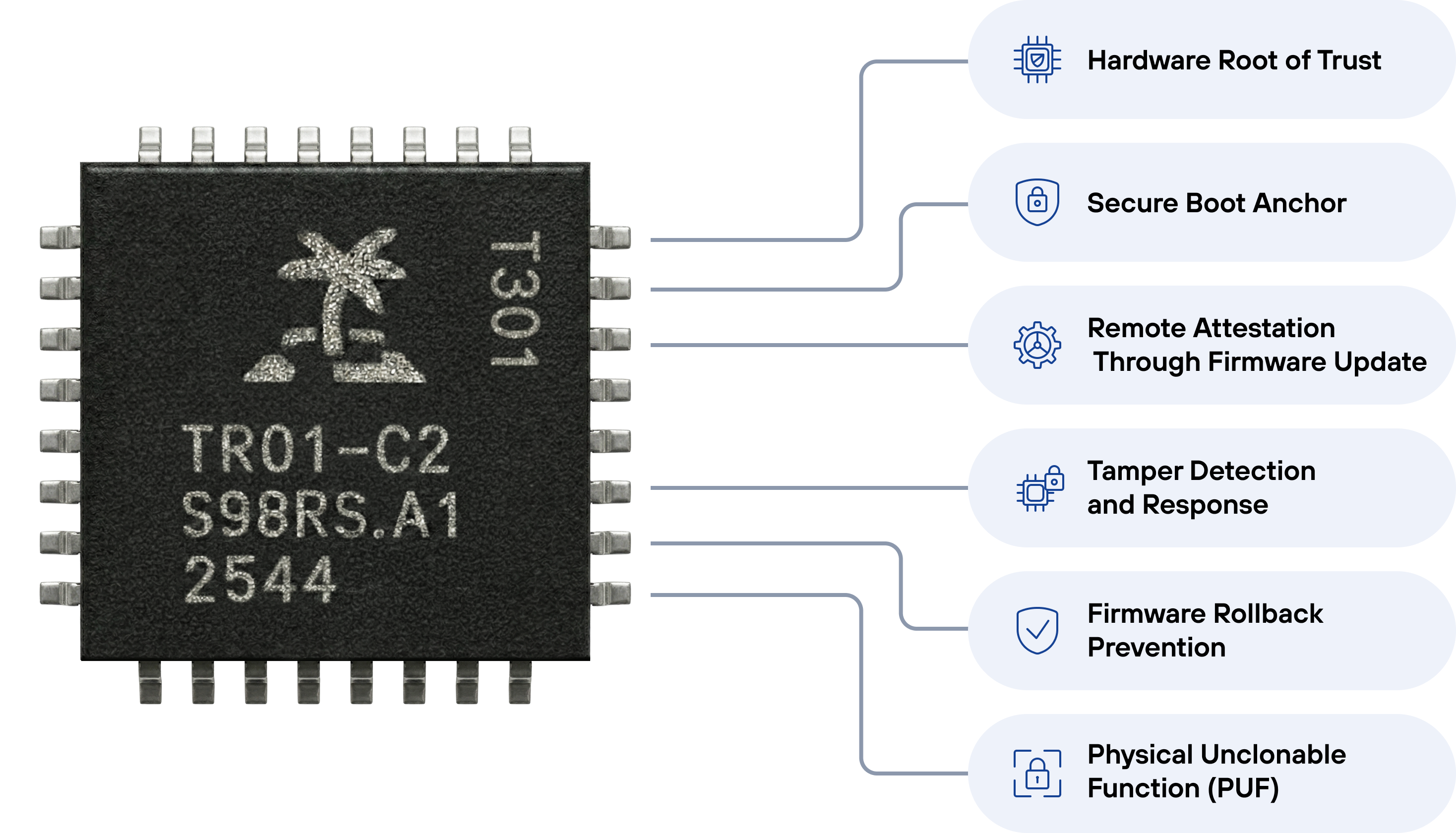
Hardware Root of Trust
How TROPIC01
Enforces Integrity
Secure Boot Anchor
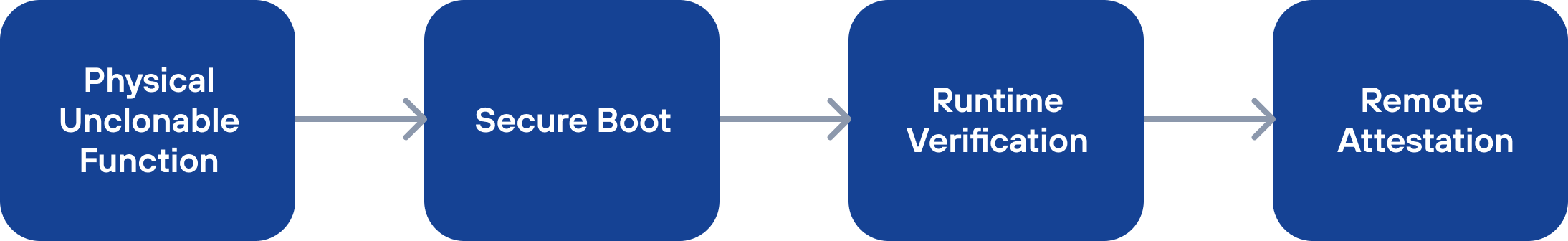
TROPIC01 stores immutable cryptographic digests and public keys in one-time programmable memory. At every boot, firmware is verified against these anchors before execution. Only signed, authenticated code can run. This prevents unauthorized firmware from executing.
Remote Attestation Through Firmware Update
TROPIC01 can provide its identity to external systems through challenge-response protocols. TROPIC01 helps remote verifiers confirm that the device is genuine, runs authentic firmware, and hasn't been compromised. This enables zero-trust architectures and supply chain verification.
Tamper Detection and Response
Hardware sensors monitor for physical attacks: voltage glitching, laser probing, electromagnetic interference, temperature manipulation. An active shield protects secure memory from invasive analysis. When tampering is detected, the chip locks down. This makes physical access significantly harder to exploit.
Firmware Rollback Prevention
Monotonic counters enforce version control for over-the-air updates. Firmware can only move forward. Combined with secure boot, this creates an unbroken chain of trust from manufacturing through every operational update.
Technical Differentiators
MAC-and-Destroy PIN Verification
Standard secure elements use PIN counters that can be glitched or reset with voltage manipulation. TROPIC01 eliminates the counter entirely. Each PIN attempt irreversibly modifies a hardware slot using Keccak-based MACs. No conditional branching operations, stored hashes, or retry logic to attack. The approach makes brute-force attempts physically impossible because the hardware state cannot be reversed.
PUF-Based Key Generation
Manufacturing variations in silicon create unique physical characteristics in each chip. TROPIC01 derives internal flash encryption keys from these variations. Keys cannot be extracted even with physical die analysis. PUF ensures that each TROPIC01 internally behaves differently, which makes cloning or replay attacks impossible.
RISC-V Auditable Architecture
TROPIC01 uses the RISC-V instruction set with complete SDK on GitHub. The hardware design, firmware, APIs, and threat model are published. Anyone can audit the security implementation. Security relies on cryptographic keys, not secret designs. This follows Kerckhoffs's principle: security should depend on keys, not on the secrecy of the mechanism.
Open Architecture, Future-Proof Security
Most secure elements hide their implementation behind NDAs and require blind trust in vendor claims. Without independent audits, vulnerabilities stay hidden and backdoors cannot be ruled out.
TROPIC01's hardware design, firmware, APIs, and threat model are published. Anyone can audit the security implementation. Independent verification becomes possible instead of required trust.
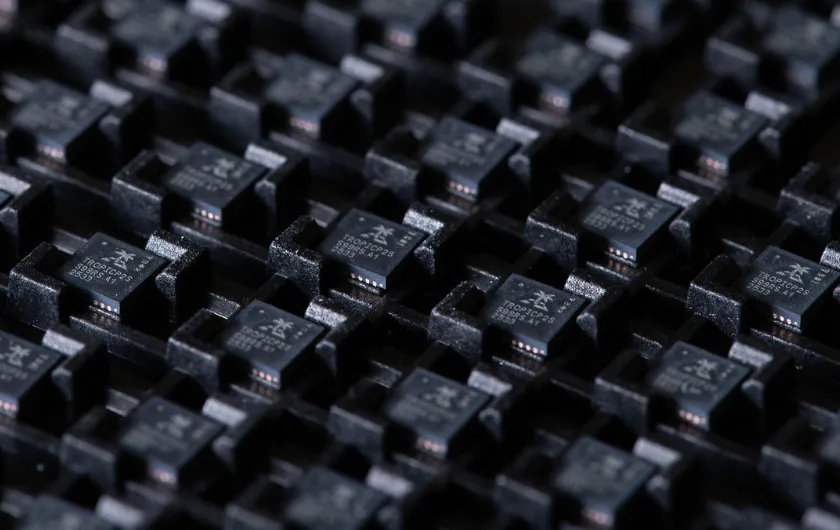
The secure chip is built with tamper-proof technology and advanced attack countermeasures to ensure robust asset protection. Its fundamental verifiability and auditability truly sets it apart with the fact that our chip actually is continuously attacked, scrutinized and probed by customers and independent security researchers.
Every attempt fuels rapid learning, firmware patches and accelerated improvements. The future-proof security is an infinite game of constant review and improvement, unlike the future-fragile security-through-obscurity chips.
Our Manifesto
We believe security-through-obscurity (blissful ignorance) in chip security has no place in this world and age and that fundamental upgrade is long overdue. We believe transparency and open design are essential for robust, sustainable security - security that evolves with the threat landscape. We believe in collaboration, and in the audacity to build a better foundation of electronic devices security.