MAC-and-Destroy PIN Verification
PIN verification that rewrites the rules of brute-force protection.
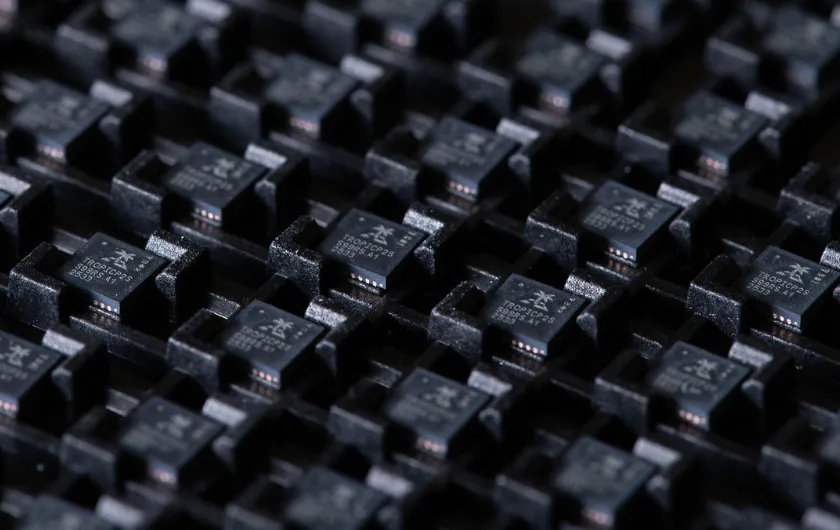
Most devices verify PINs by comparing input to a stored hash and incrementing a retry counter. Attackers bypass this by resetting counters, glitching comparisons, or rolling memory backward. The approach has known failure modes that have been exploited in the field.TROPIC01 removes the entire attack surface. There is no stored hash to extract. No retry counter to reset. Instead, each PIN attempt permanently consumes a physical hardware slot through an irreversible write operation.
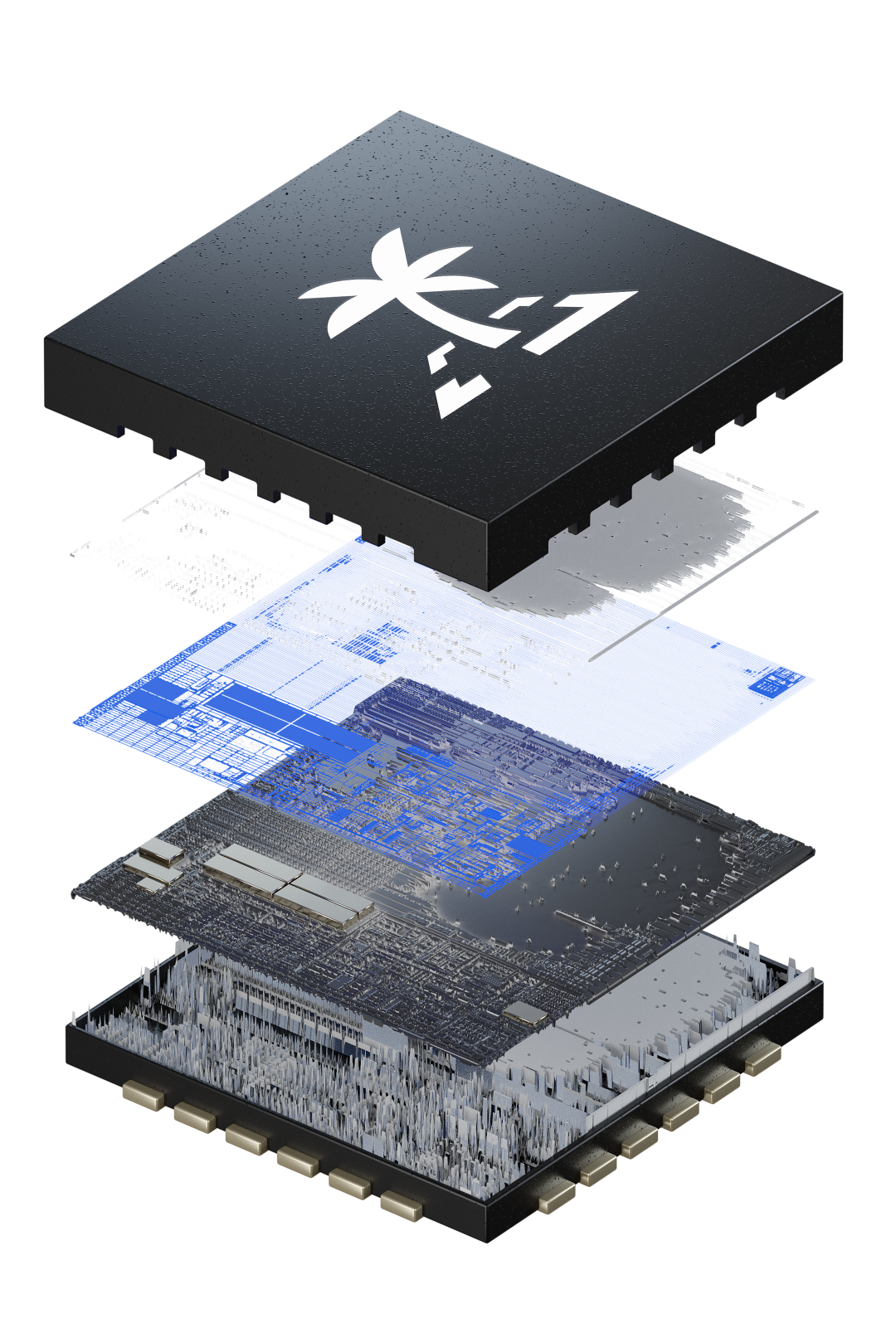
How It Works
First, a KMAC (Keccak-based Message Authentication Code) engine creates a hardware fingerprint unique to this chip and writes it into a dedicated memory slot. Writing the new value overwrites the previous slot content. The prior attempt is physically erased.
A second KMAC core combines the old slot value with the new one. If the relationship matches the expected result, the PIN is accepted. If verification fails, the slot is consumed. It cannot be retried, replayed, or reset.
The operation reads, computes, writes, and verifies in one indivisible step. Skipping any part breaks verification entirely.
Removing the Attack Surface
No Counter to Reset
Traditional retry counters use conditional logic that can be glitched. MAC-and-Destroy has no branching operations. There is no counter, no stored hash, and no comparison logic for an attacker to target.
No Rollback Possible
Each attempt permanently changes the hardware state. Voltage manipulation, memory dumps, and state restoration attacks all fail because the physical slot modification is irreversible.
Manufacturer Backdoor Protection
Each PIN is mixed at two separate cryptographic stages using chip-unique PUF keys. Even a malicious chip logging internal signals cannot reconstruct the encryption key without the high-entropy PIN. This reduces the trust placed in factories and provisioning pipelines.
Multiple PINs and Wiping PIN
TROPIC01 supports multiple independent PINs protecting the same secret. Each PIN uses separate verification data and encrypted material. The Wiping PIN acts as a panic button: it appears to be a normal PIN check, but when entered, the memory slot self-destructs to seal data under duress.

"We chose the hard way, because anything less wouldn’t cut it for securing private keys to billions of dollars and for other critical applications where security failure is simply not an option."
Instead of locking flaws behind NDAs, we built a secure chip that anyone can attack, inspect and validate. Auditable, open architecture, and free from the black boxes that breed complacency.
We don’t just tolerate scrutiny. We invite it. We encourage independent researchers, academics, and engineers to probe our chips, break them if they can, and push us to continuously improve.
Every attempted exploit drives faster patches, smarter defenses, and stronger hardware. Because security isn’t a static certificate. It’s a living process. One that must evolve as fast as the threats themselves.